LDAP
Reading time: 13 minutes
The use of LDAP (Lightweight Directory Access Protocol) is mainly for locating various entities such as organizations, individuals, and resources like files and devices within networks, both public and private. It offers a streamlined approach compared to its predecessor, DAP, by having a smaller code footprint.
LDAP directories are structured to allow their distribution across several servers, with each server housing a replicated and synchronized version of the directory, referred to as a Directory System Agent (DSA). Responsibility for handling requests lies entirely with the LDAP server, which may communicate with other DSAs as needed to deliver a unified response to the requester.
The LDAP directory's organization resembles a tree hierarchy, starting with the root directory at the top. This branches down to countries, which further divide into organizations, and then to organizational units representing various divisions or departments, finally reaching the individual entities level, including both people and shared resources like files and printers.
Default port: 389 and 636(ldaps). Global Catalog (LDAP in ActiveDirectory) is available by default on ports 3268, and 3269 for LDAPS.
PORT STATE SERVICE REASON
389/tcp open ldap syn-ack
636/tcp open tcpwrappedLDIF (LDAP Data Interchange Format) defines the directory content as a set of records. It can also represent update requests (Add, Modify, Delete, Rename).
bash
dn: dc=local
dc: local
objectClass: dcObject
dn: dc=moneycorp,dc=local
dc: moneycorp
objectClass: dcObject
objectClass: organization
dn ou=it,dc=moneycorp,dc=local
objectClass: organizationalUnit
ou: dev
dn: ou=marketing,dc=moneycorp,dc=local
objectClass: organizationalUnit
Ou: sales
dn: cn= ,ou= ,dc=moneycorp,dc=local
objectClass: personalData
cn:
sn:
gn:
uid:
ou:
mail: pepe@hacktricks.xyz
phone: 23627387495Lines 1-3 define the top level domain local
Lines 5-8 define the first level domain moneycorp (moneycorp.local)
Lines 10-16 define 2 organizational units: dev and sales
Lines 18-26 create an object of the domain and assign attributes with values
Note that if you can modify values you could be able to perform really interesting actions. For example, imagine that you can change the "sshPublicKey" information of your user or any user. It's highly probable that if this attribute exist, then ssh is reading the public keys from LDAP. If you can modify the public key of a user you will be able to login as that user even if password authentication is not enabled in ssh.
bash
If LDAP is used without SSL you can sniff credentials in plain text in the network.
Also, you can perform a MITM attack in the network between the LDAP server and the client. Here you can make a Downgrade Attack so the client with use the credentials in clear text to login.
If SSL is used you can try to make MITM like the mentioned above but offering a false certificate, if the user accepts it, you are able to Downgrade the authentication method and see the credentials again.
According to this writeup just by accessing the LDAP server with an arbitrary domain name (like company.com) he was able to contact the LDAP service and extract information as an anonymous user:
bash
LDAP anonymous binds allow unauthenticated attackers to retrieve information from the domain, such as a complete listing of users, groups, computers, user account attributes, and the domain password policy. This is a legacy configuration, and as of Windows Server 2003, only authenticated users are permitted to initiate LDAP requests. However, admins may have needed to set up a particular application to allow anonymous binds and given out more than the intended amount of access, thereby giving unauthenticated users access to all objects in AD.
If you have valid credentials to login into the LDAP server, you can dump all the information about the Domain Admin using:
bash
Using this you will be able to see the public information (like the domain name):
bash
Windapsearch is a Python script useful to enumerate users, groups, and computers from a Windows domain by utilizing LDAP queries.
bash
Check null credentials or if your credentials are valid:
bash
bash
If you find something saying that the "bind must be completed" means that the credentials are incorrect.
You can extract everything from a domain using:
bash
Extract users:
bash
Extract computers:
bash
Extract my info:
bash
Extract Domain Admins:
bash
Extract Domain Users:
bash
Extract Enterprise Admins:
bash
Extract Administrators:
bash
Extract Remote Desktop Group:
bash
To see if you have access to any password you can use grep after executing one of the queries:
bash
Please, notice that the passwords that you can find here could not be the real ones...
You can download pbis from here: https://github.com/BeyondTrust/pbis-open/ and it's usually installed in /opt/pbis.
Pbis allow you to get basic information easily:
bash
Download Apache Directory from here. You can find an example of how to use this tool here.
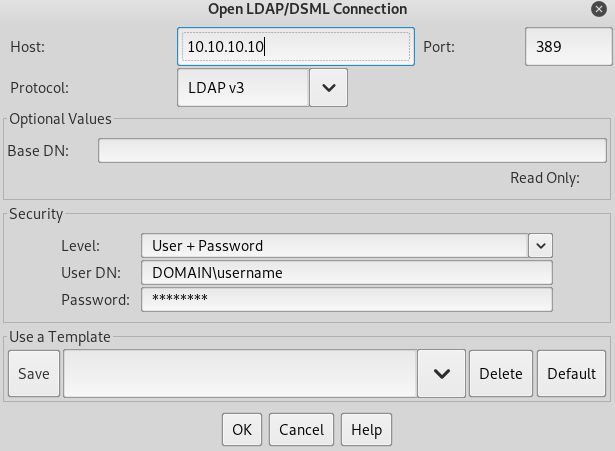
You can download a graphical interface with LDAP server here: http://www.jxplorer.org/downloads/users.html
By default is is installed in: /opt/jxplorer
Godap is an interactive terminal user interface for LDAP that can be used to interact with objects and attributes in AD and other LDAP servers. It is available for Windows, Linux and MacOS and supports simple binds, pass-the-hash, pass-the-ticket & pass-the-cert, along with several other specialized features such as searching/creating/changing/deleting objects, adding/removing users from groups, changing passwords, editing object permissions (DACLs), modifying Active-Directory Integrated DNS (ADIDNS), exporting to JSON files, etc.
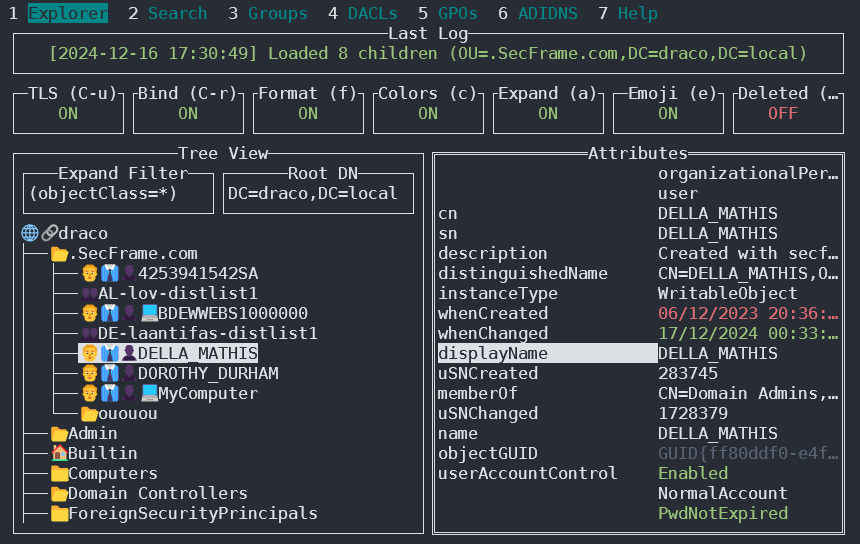
You can access it in https://github.com/Macmod/godap. For usage examples and instructions read the Wiki.
Ldapx is a flexible LDAP proxy that can be used to inspect & transform LDAP traffic from other tools. It can be used to obfuscate LDAP traffic to attempt to bypass identity protection & LDAP monitoring tools and implements most of the methods presented in the MaLDAPtive talk.
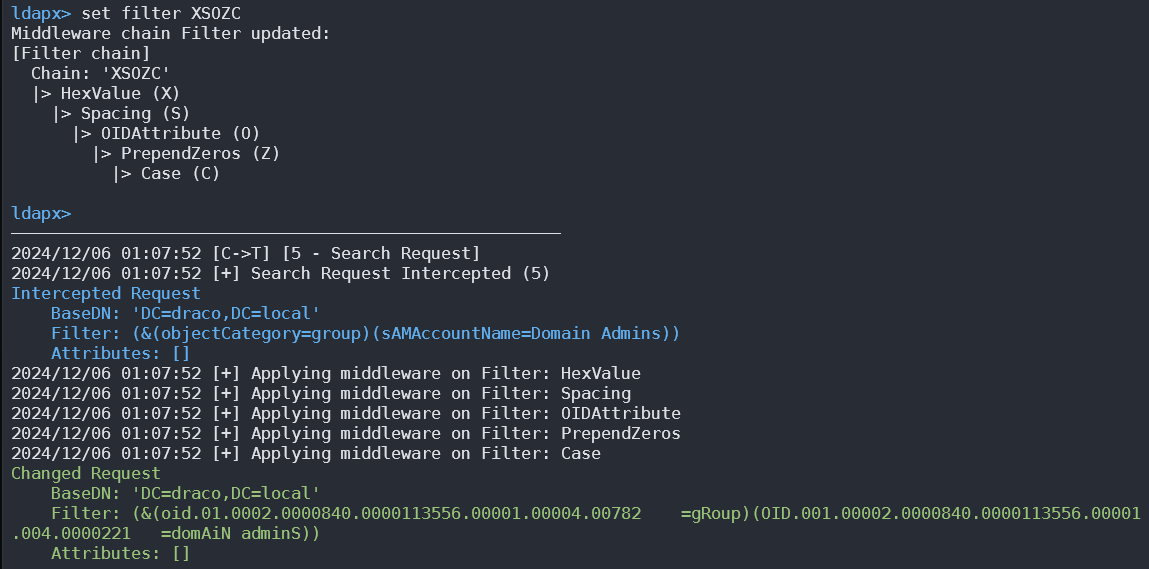
You can get it from https://github.com/Macmod/ldapx.
Using ldapsearch you can authenticate against kerberos instead of via NTLM by using the parameter -Y GSSAPI
If you can access the files where the databases are contained (could be in /var/lib/ldap). You can extract the hashes using:
bash
You can feed john with the password hash (from '{SSHA}' to 'structural' without adding 'structural').
General
containers.ldif
ldap.cfg
ldap.conf
ldap.xml
ldap-config.xml
ldap-realm.xml
slapd.conf
IBM SecureWay V3 server
V3.sas.oc
Microsoft Active Directory server
msadClassesAttrs.ldif
Netscape Directory Server 4
nsslapd.sas_at.conf
nsslapd.sas_oc.conf
OpenLDAP directory server
slapd.sas_at.conf
slapd.sas_oc.conf
Sun ONE Directory Server 5.1
75sas.ldif
Last updated